Computer Science
What we offer
News and stories
UMToday
View more news and stories-

Join us for the 2024 Computer Science Alumni and Industry Symposium
Faculty of Science
-

CBC News: Math lessons from deepfakes of Drake, other celebrities on TikTok raise concerns about misinformation
Faculty of Science, UM Today
-
Global News Winnipeg: Lack of connectivity in rural, remote Manitoba dangerous in emergencies, firefighter says
Faculty of Science, UM Today
-

Witness the spark in science when students compete for $3,000 cash prize!
Faculty of Science
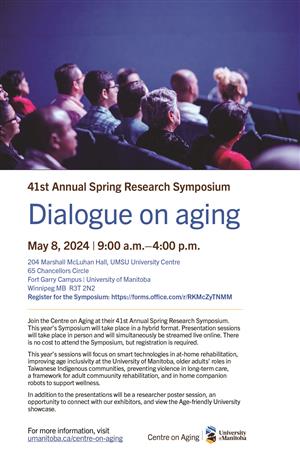
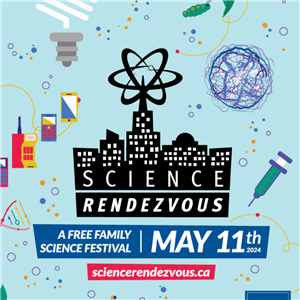
Events
You may also be looking for
For final exam viewing, please reach out to queries@cs.umanitoba.ca.
Contact us
Our office
Department of Computer Science
E2-445 EITC, 75 Chancellors Cir
University of Manitoba
Winnipeg, Manitoba, R3T 5V6 Canada
queries@cs.umanitoba.ca - General inquiries
cs.gradprogram@umanitoba.ca - Graduate Program inquiries
cs-support@lists.umanitoba.ca - Technical support for students